From Classical Secure to Quantum Safe: A Practical Roadmap for IT Leaders
Prepare for the quantum era! A roadmap for IT leaders on becoming quantum-safe. Mitigate risks with post-quantum cryptography and boost cybersecurity.
From Classical Secure to Quantum-Safe: A Practical Roadmap for IT Leaders
“When 20 million years compress into 15 minutes, your cryptographic maintenance calendar becomes a liability.”
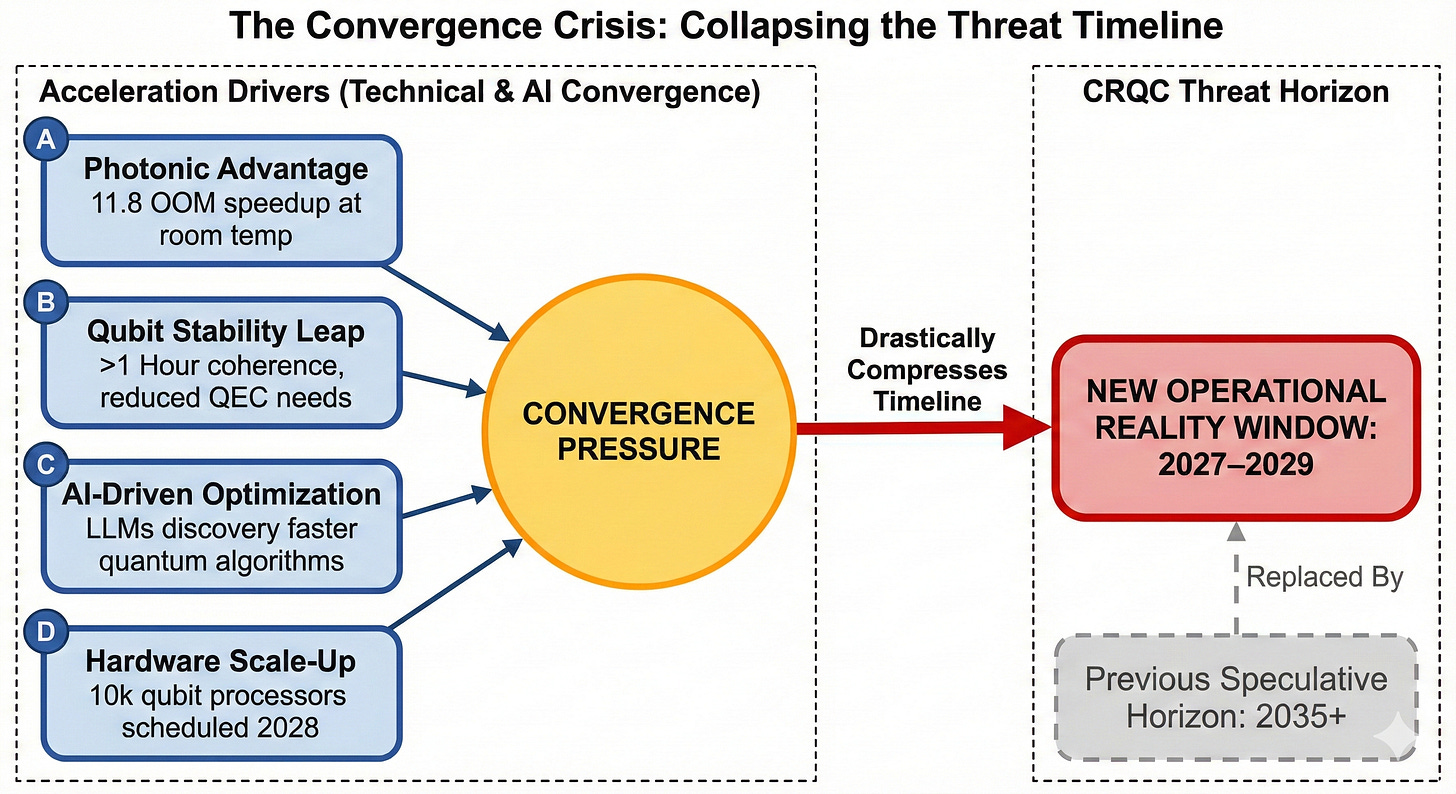
Highlight: Photonic quantum advantage, qubit stability, AI-driven quantum algorithm discovery, and hardware scale-up compress the credible threat horizon. For IT managers, post-quantum transition is an immediate, fundable program (2025–2028), not a distant research topic.
Executive Summary
Post-quantum efficient transition is an immediate priority for IT managers: inventory cryptography (CBOM), mandate crypto-agility, run practical pilots now, pressure vendors for PQC roadmaps, and apply extra controls for crown-jewel assets. Recent technical convergence—including photonic quantum systems demonstrating 11.8 orders of magnitude performance advantages, hour-long qubit stability achievements, AI-driven algorithm optimization reducing resource requirements by 1-2 orders of magnitude, and commercially available 10,000-qubit processors scheduled for 2028—compresses credible quantum threat horizons from speculative 2035+ projections to operationally probable 2027-2029 timelines (DTU, 2025; Liu et al., 2025; Quantum Zeitgeist, 2025; Interesting Engineering, 2025).
Why Quantum Threat Timelines Just Collapsed: The Convergence Crisis
Photonic Quantum Advantage Eliminates Classical Parity
The Technical University of Denmark’s demonstration of proven quantum advantage using photonic systems fundamentally altered threat assessment calculus. Researchers achieved an 11.8 orders of magnitude sample complexity reduction, solving a characterization problem in 15 minutes that would require classical systems 20 million years (DTU, 2025). Unlike superconducting platforms requiring near-absolute-zero cooling, photonic quantum computers operate at room temperature using existing optical infrastructure—suggesting adversaries can deploy quantum cryptanalytic capabilities using partially existing infrastructure rather than building entirely novel systems (Liu et al., 2025).
Million-Fold Qubit Stability Improvement Changes Error Correction Economics
Alice & Bob’s demonstration of cat qubits maintaining bit-flip stability exceeding one hour—representing a million-fold improvement over conventional superconducting transmon qubits (~25 milliseconds)—disrupts conservative CRQC timeline assumptions (Quantum Zeitgeist, 2025). Traditional quantum threat models assumed high error rates necessitating 20 million physical qubits with aggressive error correction overhead to achieve 4,096 logical qubits for RSA-2048 cryptanalysis—a scale driving 2033-2035 CRQC estimates. The hour-long coherence achievement means error correction overhead collapses by potentially 100-200×, bringing the physical qubit count for cryptanalytic applications down to 100,000-200,000 qubits—a threshold achievable by combining modular chiplet architectures by 2029-2030 (Quantum Zeitgeist, 2025).
AI-Quantum Synergy Accelerates Algorithm Optimization
Quantinuum’s collaboration with Hiverge demonstrated that Large Language Models can autonomously discover quantum algorithms achieving 1-2 orders of magnitude resource reductions compared to state-of-the-art methods (Quantinuum, 2024b). The Hive-ADAPT algorithm outperformed leading baselines while requiring exponentially fewer circuit evaluations. This AI-quantum synergy compresses the CRQC timeline from commonly cited 2030-2035 windows toward 2027-2029, as adversaries can deploy LLMs to discover optimized Shor’s algorithm variants requiring fewer qubits or lower gate fidelities than current theoretical estimates (Quantinuum, 2024b).
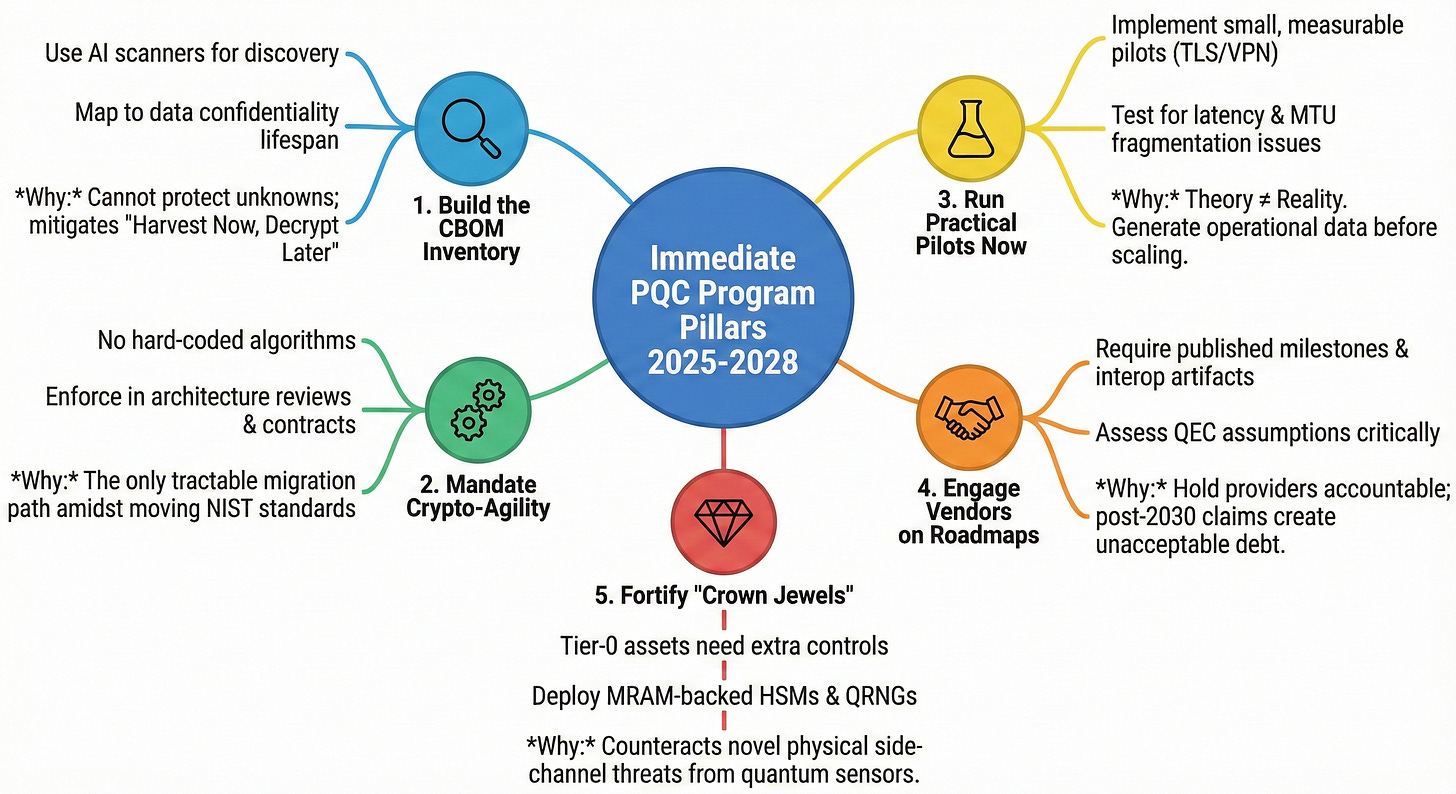
Immediate Priorities (2025-2028)
Classify and Inventory Crypto — Build a Complete Cryptographic Bill of Materials (CBOM)
What to do: Discover every use of cryptography across cloud services, on-premises systems, IoT/firmware, mobile apps, CI/CD artifacts, backups, and third-party integrations. Catalog algorithms, key lengths, key lifetimes, HSM/KMS usage, certificate chains, and long-term archives.
Why: Recent photonic quantum advantage and QEC improvements make “harvest now, decrypt later” credible; CBOM is the decision nucleus for triage. The photonic approach’s compatibility with existing telecommunications infrastructure suggests adversaries can deploy quantum cryptanalytic capabilities using partially existing infrastructure, making the 2025-2028 transition window potentially optimistic rather than conservative (Liu et al., 2025).
How (practical): Use LLM-augmented static analysis and runtime scanners, plus manual review for legacy code. Leverage GPT-style architectural models (GPT-QE, QAOA-GPT) to automate CBOM generation from legacy codebases using transformer attention mechanisms to identify classical algorithm dependencies across millions of lines of code—a task currently requiring manual audits consuming 6-18 months for large enterprises (Alexeev et al., 2025). Target 90% coverage for critical systems within 12 months.
Deliverable: CBOM database with risk tags (Tier 0/Tier 1/Tier 2), mapped to business impact and confidentiality lifespan.
Mandate Crypto-Agility Across Architecture, SDLC, and Vendors
What to do: Enforce crypto-agility as a non-functional requirement for new systems and include contractual clauses for existing vendors.
Why: Crypto-agility reduces operational disruption when swapping algorithms and becomes the tractable way to migrate in a moving standards environment (NIST PQC adoption expectations). The Hive platform’s ability to generalize across problem domains suggests crypto-agility frameworks must incorporate AI-driven continuous cryptographic assessment—treating algorithm transitions not as one-time migrations but as ongoing adaptive processes where AI monitors threat landscape evolution (Quantinuum, 2024b).
How (practical): Add pass/fail clauses in RFPs and SOWs requiring hybrid capability, HSM firmware upgradeability, and documented rollback procedures. Update architecture review checklists to block designs that hard-code crypto.
Deliverable: Procurement policy update and SDLC gating rules.
Run Practical Pilots Now — 1-2 Operational Experiments
What to do: Implement small, measurable pilots to learn real operational impacts: hybrid TLS for internal services, PQC VPNs for internal traffic, or PQC code signing in CI/CD.
Why: Pilots surface latency, message-size, HSM performance, and interoperability issues in controlled conditions; they convert theory into operational data. Alice & Bob’s stability breakthrough compresses viable attack timelines from “post-2030 theoretical capability” to “2028-2029 operational possibility” for well-resourced adversaries (Quantum Zeitgeist, 2025).
How (practical):
· Hybrid TLS pilot: instrument handshake latency, CPU/memory impact, and client compatibility matrix.
· PQC VPN pilot: measure throughput, fragmentation, rekey behavior, IDS/IPS interactions.
· Code signing pilot: measure pipeline latency and verification compatibility.
Success metrics: Handshake latency delta, throughput percentage relative to baseline, HSM latency, percentage of compatible clients. Use these to prioritize enterprise rollout.
Engage Vendors on Quantum-Safe Roadmaps
What to do: Require strategic vendors to publish PQC roadmaps with milestones, interop test artifacts, and HSM/KMS upgrade plans.
Why: Vendor claims differ in QEC and scaling assumptions; you must hold providers accountable for demonstrable interop and upgradeability. Quantinuum’s 90-qubit coherent operations with NVIDIA GPU integration signal quantum computing industry maturation to commercially viable platforms, indicating quantum threat actors will likely access quantum computing services rather than building proprietary systems (Quantinuum, 2024c).
How (practical): Issue a vendor readiness questionnaire demanding hybrid handshake traces, PQC test vectors, QRNG/HSM options, and public timelines. Score vendors; deprioritize those signaling readiness beyond acceptable windows. Organizations should assess vendor quantum-safe roadmaps against QuantWare’s 2028 availability, treating any vendor claiming post-2030 PQC readiness as creating unacceptable cryptographic debt (Interesting Engineering, 2025).
Deliverable: Vendor PQC readiness matrix.
Evaluate Additional Controls for High-Sensitivity Use Cases
What to do: For crown-jewel assets (long-retention archives, CA keys, code-signing keys), add compensating controls: QRNGs, quantum-ready HSM/KMS, physical emission hardening, and stricter key lifecycles.
Why: Quantum sensors and biological qubit sensors create new side-channel threats—physical resistance and QRNG entropy are practical mitigations (CBS News Chicago, 2025). University of Chicago’s demonstration of enhanced yellow fluorescent protein (EYFP) functioning as optically addressable spin qubits inside living cells creates potential for quantum-enhanced hardware exploitation where adversaries deploy biological quantum sensors to extract cryptographic keys from electromagnetic emanations (CBS News Chicago, 2025).
How (practical): Purchase quantum-ready HSMs for Tier-0 keys, insist on QRNG as an option, and include emission-resistance testing in hardware acceptance. Leverage spintronic MRAM for secure key storage—TU Delft’s demonstration of quantum spin currents in graphene enables ultrathin spintronic circuits providing quantum-resistant data persistence architectures immune to cold-boot attacks and power-analysis side channels (TU Delft, 2025).
Deliverable: Crown-jewel control map and procurement spec.
Operational Guidance
Treat PQC as a Near-Term Program
Programize: Assign program sponsor (CISO/Head of IT), dedicate a Program Lead and skeleton cross-functional team (architecture, DevOps, procurement, legal).
Budget: Secure multi-year funding and contingency for HSM replacements and lab testing.
Governance cadence: Weekly execution, monthly steering, quarterly board reporting.
Integrate Crypto-Agility into Procurement, Architecture Reviews, and Testing Pipelines
Procurement: Default to vendors with PQC roadmaps and interop artifacts; require firmware upgradeability for HSMs.
SDLC: CBOM automation gates in CI/CD; crypto unit tests should support dual-stack verification.
Testing: Maintain a PQC test lab (internal or partner) replicating production stacks for full-stack interoperability testing.
Measure Pilot Outcomes to Inform Broader Rollouts and Risk Prioritization
Scorecard: Latency deltas, throughput deltas, HSM latency, client compatibility rate, operational complexity.
Use pilot scorecards to create a prioritized migration queue tied to business impact.
Target State for 2026
By 2026, a mature IT posture should include:
· Documented enterprise PQC roadmap endorsed by the board.
· CBOM coverage across critical systems (target ≥90%).
· Crypto-agility enforced across SDLC and included in all new vendor contracts.
· At least one validated live PQC pilot (e.g., hybrid TLS or PQC VPN) with operational scorecard and runbook.
· Vendor ecosystem with documented PQC interop test artifacts and firmware upgrade paths for HSMs/KMS.
Phased Approach to Post-Quantum Transition
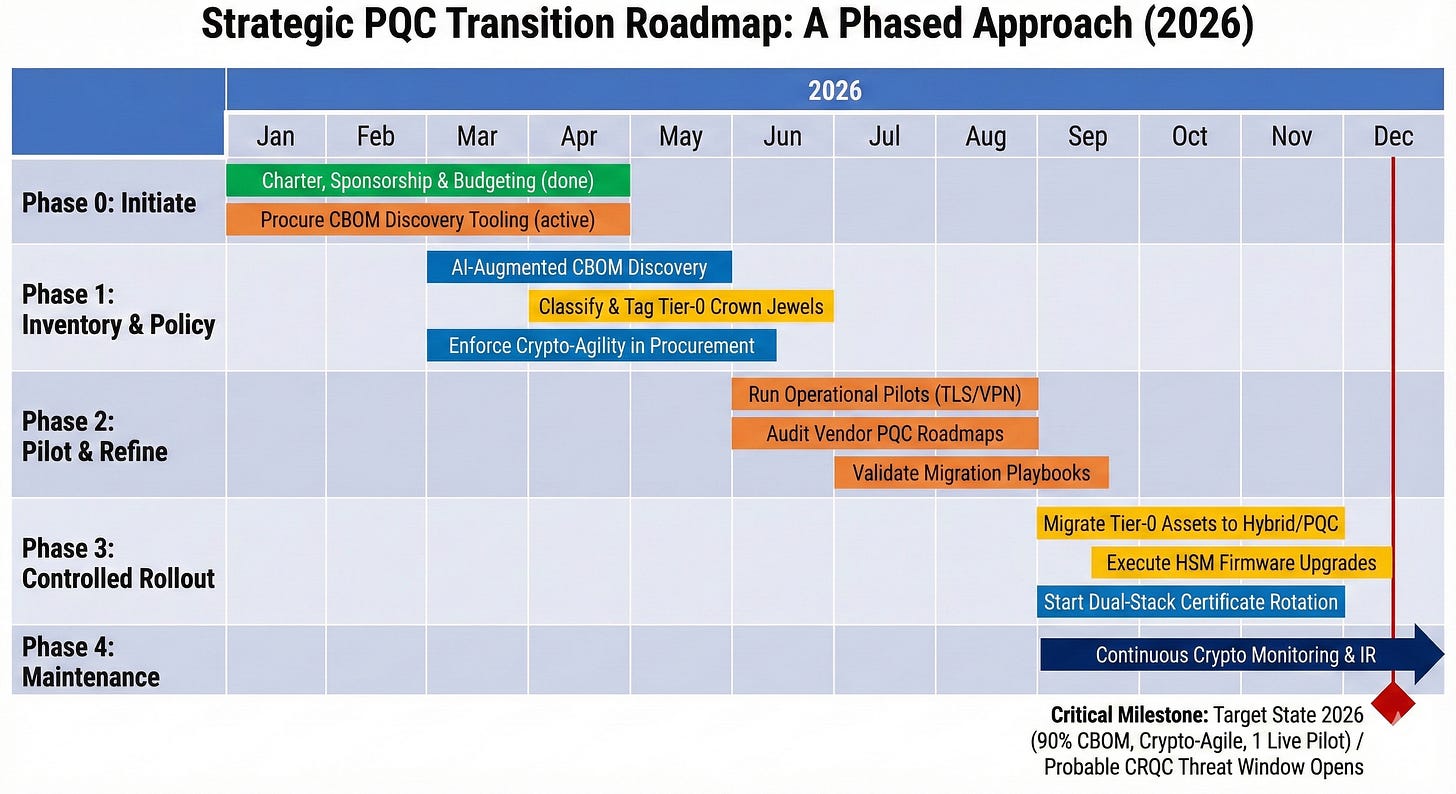
Strategic PQC Transition Roadmap: 12-Month Timeline (2026)
The chart above presents a compressed, 12-month critical-path view of the five-phase PQC program, all contained within the 2026 calendar year. This timeline balances the full program structure with the practical reality that organizations need to see concrete progress and measurable output by year-end, especially given the compressed threat window.
Phase-by-Phase Breakdown for 2026
Phase 0 — Initiate (January–March)
Program launch and tooling procurement must complete in Q1. Secure board sponsorship, finalize multi-year budget, and procure CBOM discovery platforms that can use AI-augmented static analysis. By end of March, establish the PQC pilot team and scope the first operational experiment (e.g., hybrid TLS for internal infrastructure). This foundation eliminates delays downstream.
Phase 1 — Inventory & Policy (March–August)
Overlapping with Phase 0, CBOM discovery and classification run April through June using AI tools to scan repositories, container images, and firmware. By July, Tier-0 “crown jewels” (long-lived archives, CA keys, code-signing keys) should be classified and tagged for immediate compensating controls (QRNG, MRAM HSMs, emission hardening). Simultaneously, procurement policy and SDLC gating rules enforcing crypto-agility must be rolled out to all active RFPs and vendor contracts by June.
Phase 2 — Pilot & Refine (June–October)
By June, hybrid TLS pilot should launch in a representative production segment (e.g., internal services with known client ecosystem). Measure handshake latency, CPU/memory footprint, and compatibility rates. In parallel, audit top strategic vendors on their PQC roadmaps, asking for QEC assumptions, AI-validation transparency, and HSM firmware upgrade paths. By September, produce pilot scorecards and detailed migration playbooks documenting performance, interop issues, and lessons learned.
Phase 3 — Controlled Rollout (September–December)
Early migration of Tier-0 assets to hybrid constructions begins in October, informed by pilot data. October-November sees HSM firmware upgrades validated in the test lab. December kicks off dual-stack certificate rotation with careful rollback planning. These actions must be complete enough by year-end to demonstrate real momentum to boards and regulators.
Phase 4 — Continuous Maintenance (October 2026 onwards)
Continuous cryptographic monitoring and quarterly PQC reporting begin in Q4 2026 and extend indefinitely. This phase encompasses ongoing CBOM updates, re-certification of vendors as new PQC standards emerge, and integration of PQC scenarios into incident-response tabletops.
Critical Milestone: End of 2026 Target State
By December 31, 2026, organizations following this roadmap should have:
· 90% CBOM coverage for Tier-0 and Tier-1 assets
· Crypto-agility enforced in procurement, SDLC, and architecture reviews
· At least one validated operational PQC pilot with documented scorecard and runbook
· Vendor ecosystem assessment showing which partners have credible PQC/QEC/AI-validation stories and which do not
· Hardware foundation upgrades underway for HSM/KMS with MRAM, QRNG, and firmware upgrade capabilities
NIST PQC Standards Adoption Plan (Practical Steps)
· Monitor NIST announcements and align pilot selections to candidate algorithms they endorse.
· Use hybrid constructions during standardization uncertainty: combine classical algorithms with PQC candidates to create defense-in-depth.
· Validate against NIST test vectors and interoperability suites as they are released.
Interoperability Challenges in Quantum-Safe Rollout (What Breaks and How to Manage It)
Message size & MTU: PQC KEMs and signatures can increase packet sizes, causing fragmentation and NAT issues—test for fragmentation and MTU negotiation.
Handshake and middlebox behavior: Expanded handshakes and hybrid structures can trigger middlebox timeouts and DPI rejection—test across network paths.
HSM firmware & key formats: PQC often requires new key formats and firmware support—insist on secure firmware update mechanisms and rollback.
PKI churn and certificate lifetimes: Longer or shorter lifetimes affect revocation windows and reissuance cycles—plan certificate rollover windows proactively.
Client ecosystem compatibility: Embedded devices and legacy clients may fail—map compatibility and plan graceful fallbacks.
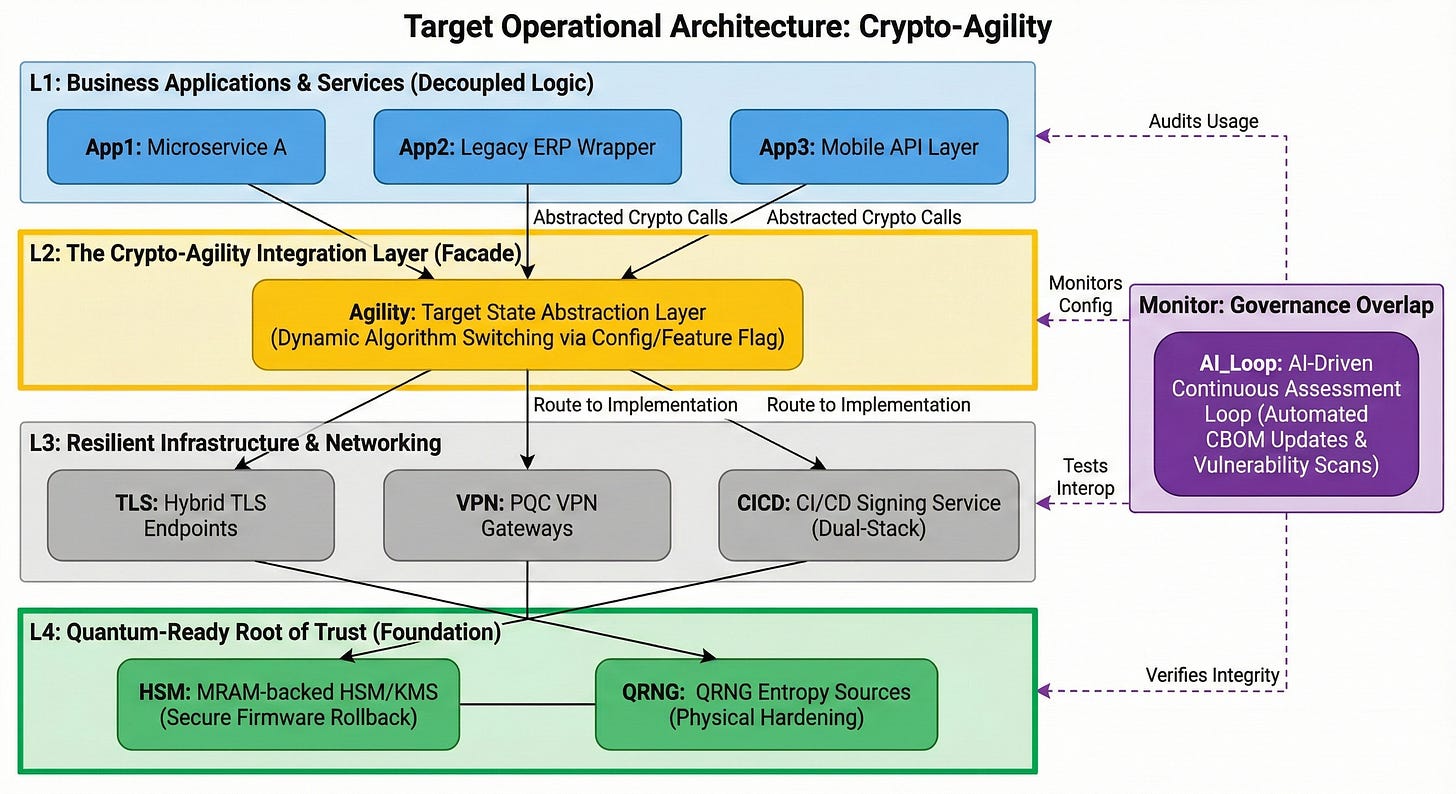
Crypto-Agility Strategy for Enterprise IT (Operational Design Patterns)
Design for Dual-Stack (Hybrid) from Day One
Architectural pattern: Support simultaneous classical + PQC signatures/KEMs for critical transactions to maintain backward compatibility while enabling forward migration.
Decouple Algorithm Choice from Application Logic
Architectural pattern: Use a cryptographic abstraction layer (crypto facade) within services so algorithms can be swapped by configuration/feature flag without redeploying business logic.
Centralize Key Lifecycle Management
Operational pattern: Centralized KMS/HSM handling for all key types with automated rotation, dual-stack wrapping, and key-usage policies.
Continuous Cryptographic Assessment
Operational pattern: Integrate CBOM updates and cryptographic tests into CI/CD, with alerts on new cryptographic usage or outdated algorithms. Deploy AI-driven continuous cryptographic assessment using reinforcement learning methods that translate to adaptive cryptographic key management where RL agents dynamically adjust key rotation schedules based on real-time threat intelligence (Alexeev et al., 2025).
Becoming Quantum Safe: Protect Your Business and Mitigate Risks with Post-Quantum Cryptography and Crypto-Agility
Tactical Example: Migrating Code Signing
Why: Code signing compromise can allow update forgery and supply-chain compromise.
How (practical): Dual-sign artifacts (classical + PQC), update client verification to accept hybrid signatures, rotate signing keys in HSM partitions with PQC support, and test rollback strategies.
Tactical Example: Protecting Long-Term Archives
Why: “Harvest now, decrypt later” makes archived data vulnerable, with China accused of systematically stealing encrypted data for post-Q-Day decryption (First Movers, 2025b).
How (practical): Envelope encryption with PQC KEM for new archives; for existing archives, encrypt new master keys under quantum-ready HSMs and plan re-encryption windows based on risk appetite.
Operational Checklists
CBOM Quick Checklist
· Crawl repos, images, firmware.
· Identify crypto primitives, key storage, and key lifetimes.
· Produce asset-risk map and migration priority list.
Hybrid TLS Pilot Quick Checklist
· Deploy hybrid server certs.
· Test clients across matrix.
· Measure latency, CPU, handshake success rate.
· Validate rollback and fallback behaviors.
PQC VPN Pilot Quick Checklist
· Deploy PQC gateway & client.
· Generate traffic mixes.
· Measure throughput, fragmentation, rekey.
· Test IDS/IPS compatibility.
Vendor PQC Questionnaire (Core Items)
· Do you have a PQC roadmap? (timeline, milestones)
· Have you completed hybrid TLS/VPN interop testing? Provide traces.
· Do your HSMs support firmware upgrade with PQC key formats?
· Do you provide QRNG options or support?
· Have you used AI tools to validate PQC implementations?
Extra Operational Considerations
Cost & Resource Planning
HSM/KMS upgrades and test lab time will be the primary capital and OPEX pressures. Budget early to avoid supplier backlogs.
People & Skills
Upskill crypto architects and DevOps engineers on PQC primitives, hybrid patterns, and interop testing. Consider external consultancy for initial pilots.
Regulatory & Compliance
Expect regulators to include PQC readiness in security audits. Map PQC program outcomes to compliance frameworks.
Incident Response & Forensics
Update IR playbooks for PQC-related incidents (compromise of PQC transitions, failed rollbacks, HSM firmware issues) and include post-quantum test cases in tabletop exercises.
Non-Obvious Insights
Prioritize CBOM Quality Over Immediate Mass Migration
High‑quality CBOM is the main force multiplier of the PQC program. A precise inventory lets you target Tier‑0 and Tier‑1 systems first, align pilots with real business risk, and avoid “bad‑wide” migrations that are expensive, brittle, and still leave gaps.
Practically, this means enriching the CBOM beyond “where crypto is used” to “which data has long confidentiality lifetimes, which algorithms and key lengths protect it, which vendors and components are involved, and how painful it will be to change them.” That level of detail allows you to choose pilots and migration waves based on impact per engineering hour, instead of guessing or following vendor marketing cycles.
Expect Vendor PQC Claims to Contain Optimistic QEC Assumptions
Most vendor PQC timelines are built on optimistic assumptions about error rates and error‑correction overhead. Those QEC parameters determine whether a cryptanalysis‑grade quantum machine is a 2035 problem for superpowers or a 2029 problem for well‑funded actors.
IT leaders should avoid anchoring on bare calendar claims like “safe until 2035.” Instead, ask vendors what physical error rates, code families, and logical‑qubit counts they assume, and how sensitive their timelines are if those parameters improve faster than expected. If a vendor cannot articulate this, or relies mainly on “we think it’s far away,” treat that as a risk flag and plan your own PQC timeline accordingly.
MRAM/Spintronic Components Provide Immediate Operational Value
MRAM and spintronic components are one of the few infrastructure moves that pay off immediately, regardless of which PQC algorithms win. Larger PQC key sizes and more stateful protocols put pressure on memory and key storage; moving Tier‑0 keys into MRAM‑backed HSMs reduces cold‑boot and power‑analysis exposure while handling larger keys more comfortably.
Because spintronic devices are non‑volatile and energy‑efficient, they also help absorb the extra computational and monitoring load introduced by PQC and AI‑driven cryptographic testing. Building MRAM/spintronic requirements into HSM/KMS refresh cycles between 2025 and 2027 gives you both a stronger hardware root of trust and better energy headroom for future quantum‑aware workloads.
Dual Use of AI: Require Vendors to Publish How They Used AI to Validate PQC Implementations
AI now sits on both sides of the cryptographic chessboard. Attackers can use LLMs, RL, and graph models to search for protocol flaws and side channels faster than manual testing ever could. Defenders can use the same techniques to extract CBOMs from large codebases, generate fuzz cases, and continuously test PQC implementations under realistic stress.
Because of this dual use, “we use PQC” is not sufficient reassurance from a vendor. Ask how they used AI in development and testing: which models, on which parts of the stack, how often those tests run, and what kinds of issues they have surfaced. Internally, treat AI‑based cryptographic analysis as a standard control baked into CI/CD and security testing, not an experiment living in a lab.
Physical Security Becomes Cryptographic Security
Advances in quantum and biological sensors weaken the old assumption that many side‑channel attacks are “theoretical only.” Highly sensitive sensors make it easier to infer keys from subtle electromagnetic, power, or timing emissions, even when algorithms and protocols are mathematically sound.
That shifts HSM/KMS evaluation into a joint physical‑and‑cryptographic exercise. Procurement and acceptance tests should explicitly assess emission resistance, shielding, tamper resistance, and susceptibility to realistic side‑channel techniques. Facilities, hardware, and security teams need shared playbooks for detecting suspicious sensing devices around critical infrastructure. In a quantum‑aware world, a cryptosystem that is mathematically strong but physically leaky is not actually secure.
Reflection
The post‑quantum challenge is not just “a new set of algorithms” but a convergence of trends: faster‑than‑expected quantum hardware progress, AI‑assisted optimization, more powerful sensing, and growing evidence of long‑term data harvesting. Treating this as a distant research topic underestimates both the technical momentum and the fiscal risk of inaction on long‑lived sensitive data.
However, the most effective response still looks like disciplined engineering, not emergency heroics. The winning pattern is: build a reliable CBOM, run small but realistic pilots, pressure vendors with concrete questions and requirements, strengthen hardware foundations, and measure everything. This approach makes PQC part of ongoing infrastructure lifecycle management rather than an exceptional, one‑time “big bang” change.
Crucially, the downside of moving early in a measured way is bounded—some extra engineering, hardware refresh, and pilot overhead—while the downside of waiting too long is unbounded and irreversible for archived or highly regulated data. Even if quantum timelines slip, organizations that build crypto‑agility, better key management, and stronger vendor governance now will end up with cleaner, more resilient security architectures across both classical and quantum threat scenarios.
Key Takeaways
Immediate (Next 30 Days)
· Appoint a PQC Program Lead with clear sponsorship and scope (CBOM, pilots, vendor and hardware strategy).
· Send a PQC and QEC/AI‑validation questionnaire to top strategic suppliers and critical cloud/HSM providers.
· Procure CBOM automation (including AI‑assisted analysis) and identify Tier‑0 systems and data with long confidentiality lifetimes.
Near Term (Next 90 Days)
· Bring Tier‑0 CBOM to decision‑grade quality and use it to choose the first 1–2 pilots.
· Embed crypto‑agility into new designs and contracts: no hard‑coded algorithms, mandatory upgrade paths, and hybrid‑ready interfaces.
· Define pilot success metrics that cover performance, interoperability, operational complexity, and basic side‑channel/AI‑testing coverage.
Mid Term (Next 180 Days)
· Execute PQC pilots (e.g., hybrid TLS, PQC VPN, or code signing) on CBOM‑prioritized systems, not just low‑risk sandboxes.
· Turn pilot results into migration playbooks and scorecards that guide which systems move next, and how.
· Start HSM/KMS refresh planning with explicit evaluation of MRAM/spintronic options, QRNG support, firmware updatability, and emission‑resistance properties.
Governance (Ongoing)
· Report quarterly to the board using clear, non‑sensational metrics: CBOM coverage and quality, pilot status, vendor PQC/QEC/AI transparency, and hardware refresh progress.
· Maintain a PQC test lab and schedule regular interoperability and regression tests as standards, implementations, and AI‑based testing tools evolve.
· Treat PQC as continuous lifecycle work: keep updating CBOM, crypto‑agility patterns, AI‑based testing, and physical side‑channel defenses as part of normal change and architecture governance.
If your organization needs expert guidance to move from classical secure to quantum‑safe and a practical roadmap for it leaders, contact our experienced consulting team today — we provide tailored assessments, prioritized roadmaps, pilot and full implementations, and compliance-ready plans that minimize risk and protect business-critical systems. Book a complimentary strategy session now to get a clear timeline, cost estimate, and step-by-step actions you can apply immediately; email Thomas directly at tp@compris.com or click to schedule a call and start your transition with confidence.
Co-authors
Thomas Poetter , Founder & CEO of Compris Technologies AG with an IQ of 140, graduated as master of computer science from the University of Kaiserslautern (at the time the only opportunity to study AI, today called RPTU) with artificial intelligence (AI) and natural language processing (NLP) as key focus areas. Working with DFKI (German Research Center for Artificial Intelligence) during his studies, Thomas was the only German AI graduate around the year 2000, one of the first entrepreneurs who received in 1998 a 2 years’ start-up stipend from the Fraunhofer society, in his case from the Fraunhofer Institute for Experimental Software Engineering (IESE). Inspired by Fraunhofer’s success with MP3, Thomas achieved a comparable success with his 8 patents around innovations for watermarking text-based contents (eBooks, documents, web pages, etc.) and for secret inconspicuous communication. His business plans received 3 awards and €40k in prize money, among them 2nd best in Germany (VW’s Promotion startup contest) and Thomas was 2x best German participant of the business French contest “Golden Word” (Mot d’or with over 30 000 participants). The patents are nowadays being used by IBM, SAP/Sybase, Amazon, Intel, Microsoft, Nuance, Fuji Xerox, AT&T, Amazon, Fraunhofer, Yandex, Adobe, Discord, Certicom and many others. He with his company since then has successfully helped 13 DAX30 corporations, the German government and more than 100 international Fortune 500 corporations making each project a success and achieving significant innovations in the fields of AI, IT architecture, cybersecurity, big data and artificial intelligence – improving the lives of more than a billion people. His publications have achieved more than 30 000 downloads, ranking him in the top third of all researchers in spite of never ever having gotten research subsidies like most of the researchers.
Renato Azevedo Sant Anna is an AI Product Leader & Innovation Architect, author, and strategic consultant recognized for his interdisciplinary profile and ability to connect technology, business, and strategy. With a background in Computer Engineering and specializations in Marketing (FGV), Analytics and Big Data (FIA), Digital Business (USP/Esalq), and Entrepreneurship (Unesp), he combines deep technical expertise with sharp market insight. He leads digital transformation and AI strategy initiatives for Retail, Technology, and SaaS companies, applying business design to create differentiated strategies and Go-To-Market (GTM) plans that improve operational efficiency and generate concrete business outcomes. Renato is the author of “Forjando Carreiras com IA”, co-author of an article in Forbes USA, and has served as a judge at DeveloperWeek Hackathon 2025, besides speaking at national and international events on AI Strategy and AI for Business. He is also the creator of the “11 Laws of Collaborative AI,” a manifesto that defends governed, human-centered AI as a driver of responsible innovation. As a mentor, he applies a unique methodology that blends the OODA Loop, agile practices, and Design Thinking to help organizations build sustainable value. His mission is to guide companies through digital transformation, proving that innovation is not optional—it is the foundation of a prosperous and sustainable future.
References
Alexeev, Y., et al. (2025). Artificial intelligence for quantum computing. Nature Communications. https://www.nature.com/articles/s41467-025-65836-3
CBS News Chicago. (2025). University of Chicago researchers use biological protein to build quantum sensor. CBS News. https://www.cbsnews.com/chicago/news/university-of-chicago-researchers-biological-protein-quantum-sensor/
DTU. (2025). Proven quantum advantage: Researchers cut the time for a learning task from 20 million years to 15 minutes. Technical University of Denmark News. https://www.dtu.dk/english/newsarchive/2025/09/proven-quantum-advantage_researchers-cut-the-time-for-a-learning-task-from-20-million-years-to-15-mi
First Movers. (2025a). Scientists just did 20 million years of work in 15 minutes (This changes everything) [Video]. YouTube.
First Movers. (2025b). QUANTUM WILL ECLIPSE AI: Why everyone’s betting on the wrong horse [Video]. YouTube.
First Movers. (2025c). Spintronics: Less energy demand [Video]. YouTube.
Interesting Engineering. (2025). World’s first 10,000-qubit processor marks 100× quantum scaling leap. Interesting Engineering. https://interestingengineering.com/innovation/quantware-qpu-10k-qubits
Liu, Z., et al. (2025). Quantum learning advantage on a scalable photonic platform. Science. https://www.science.org/doi/10.1126/science.adv2560
Quantinuum. (2024a). From memory to logic. Quantinuum Blog. https://www.quantinuum.com/blog/from-memory-to-logic
Quantinuum. (2024b). Automated quantum algorithm discovery for quantum chemistry. Quantinuum Blog. https://www.quantinuum.com/blog/automated-quantum-algorithm-discovery-for-quantum-chemistry
Quantinuum. (2024c). Helios delivers quantum advantage with real-world impact. Quantinuum Blog. https://www.quantinuum.com/blog/helios-delivers-quantum-advantage-with-real-world-impact
Quantum Zeitgeist. (2025). Alice & Bob cat qubits achieve hour-long bit-flip resistance, nearing 2030 roadmap goals. Quantum Zeitgeist. https://quantumzeitgeist.com/alice-bob-cat-qubits-achieve-hour-long-bit-flip-resistance-nearing-2030-roadmap-goals/
TU Delft. (2025). Breakthrough in spintronic devices for ultra-thin quantum circuits. TU Delft News. https://www.tudelft.nl/en/2025/tnw/breakthrough-in-spintronic-devices-for-ultra-thin-quantum-circuits